Securing applications and data across multiple cloud environments calls for consistent security measures and access controls, not to mention taking the extra effort around compliance requirements. In this context, Kubernetes multi cloud cluster security seems like a mountain towering over us in its immensity. But if you find a way to scale it, the view from the top will be worth it.
The heterogeneous nature of multi cloud complicates a lot of things but also has some security advantages.
Still, don’t forget that every cloud provider has their own security controls and configurations, leading to potential inconsistencies in policy enforcement.
Here’s a guide to achieving Kubernetes multi cloud cluster security despite the sheer diversity of security and compliance requirements you’re facing.
7 security challenges of multi cloud Kubernetes
1. Multi- or single-cloud, Kubernetes security is already a challenge
By default, Kubernetes allows communication between applications and services. While this improves integration, it also broadens the attack surface.
On top of that, Kubernetes deployments are dynamic and complicated, with containers being created, modified, and deleted on a regular basis. This continual change makes it difficult to keep a clear picture of your current security posture, especially when deployments are dispersed across many clouds.
A one-size-fits-all approach to security is bound to fail in a multi cloud environment due to its complexity. What teams need is a consistent security approach that takes into account the inherent security risks of Kubernetes and the complexities of a multi cloud arrangement.
2. Lack of consistent security policy
Each cloud service provider has unique security safeguards in place.
For example, Azure provides AKS with a Hardened access tier, which gives the full range of Azure security capabilities at a premium.
Also, operational security responsibilities might vary substantially depending on the provider. This unpredictability has the potential to result in lock-in situations.
3. Network security
Kubernetes network settings may differ significantly between cloud environments, demanding from teams a thorough understanding of each system to provide the right security configurations.
Users must protect their own cloud resources under the shared responsibility concept. And teams need to be consistent in establishing and administering their security protocols, including shutting down their network settings, to properly secure their cloud environments.
4. Data protection and privacy
Another thing you need to look after is the data saved and managed in your Kubernetes multi cloud cluster. Encrypting secrets, ensuring effective access control, and taking extra care about the proper configuration for any extra workloads are all key here.
5. Identity and Access Management
IAM is an important part of multi cloud security. In the case of a multi cloud Kubernetes cluster, it may become troublesome owing to different cloud infrastructures and access control systems.
Let’s not forget that Kubernetes offers its own access control methods, which the majority of cloud providers don’t properly regulate. This adds more complexity to security strategies.
6. Monitoring and visibility
Visibility into your Kubernetes deployments across all cloud environments is critical for efficient issue monitoring and response.
But don’t expect this to be an easy feat. Each cloud provider has its own set of monitoring tools and services that may or may not work well together. Naturally, this makes maintaining a uniform view of your system’s state even more challenging.
7. Compliance
Another challenge with multi cloud Kubernetes compliance is that providers may use different compliance procedures and reporting techniques. This puts more strain on teams looking to guarantee conformity across contexts.
Furthermore, the number of controls that enable these rules may vary depending on the provider. All of this might lead to unexpected gaps in compliance.
This calls for investing time and work into properly understanding and accounting for these differences to maintain strong compliance in multi cloud settings.
Best practices for managing security in a Kubernetes multi cloud cluster
1. Ensure that secure setups are in place
By default, Kubernetes has various security features, such as the ability to run containers as Network Policies and Pod Security Admission.
Since they’re typically not turned on by default, it might be necessary to configure these capabilities manually.
Double-check that they’re all set to take advantage of these features.
2. Set up network policies and segmentation
Kubernetes security relies heavily on network constraints and segmentation. By limiting traffic between your pods, network policies reduce the potential attack surface and prevent lateral movement within your cluster.
Consider segmenting your Kubernetes deployments by environment (dev, test, prod) or data sensitivity and using separate namespaces per application or service. It’s important to limit access to only the necessary connections for both egress and ingress.
3. Implement resource quotas and set ranges
Kubernetes has tools such as resource quotas and limit ranges to regulate the resources (CPU, memory, storage, etc.) that a namespace or pod may use.
Enforce Kubernetes resource limits to avoid resource depletion attacks and ensure that no one application or user can monopolize your cluster’s resources.
4. Regular audits and monitoring should be implemented
Regularly audit your Kubernetes clusters to identify and remedy any misconfigurations or vulnerabilities. You should also implement rigorous monitoring to keep track of the state of your system and notice any unusual behavior as soon as feasible.
A centralized logging solution helps you gather and analyze logs from all of your cloud environments in one location.
5. Use namespaces to segregate critical workloads
Kubernetes namespaces allow you to divide your workloads, which can be useful for security processes.
You can use namespaces to separate sensitive activities or environments and implement suitable role-based access control (RBAC) restrictions at the namespace level.
Jump-start your security configuration by following this guide: Kubernetes Security: 10 Best Practices from the Industry and Community
Kubernetes security tools and strategies for multi cloud setups
Let’s have a look at some tools and ways you can use to implement these best practices and increase your multi cloud Kubernetes cluster security.
RBAC (Role-Based Access Control)
RBAC is a fundamental component of Kubernetes security, which determines who has access to which resources via the Kubernetes API and how those users interact with those resources based on their responsibilities.
RBAC assists in enforcing the idea of least privilege, reducing the risk of unauthorized access or activities.
However, when the number of roles grows, the process gets more sophisticated, culminating in something known as role explosion. You don’t want to end up there.
Tools for managing secrets
Tokens, passwords, and certificates require secret management to be secure.
Tools like HashiCorp Vault and AWS Secrets Manager allow encryption, secure storage, and fine-grained control over access to this data.
By using such solutions, you can lower the risk of a breach and safeguard crucial data from being exposed.
Pod Security Admission
Kubernetes has an admission controller called Pod Security Admission. This controller is essential for establishing and enforcing the security restrictions that a pod must meet in order to function in the cluster.
This includes options like running containers in non-privileged mode and other security measures for your Kubernetes clusters.
Tools for cloud provider security
Using your cloud provider’s native security solutions may provide an additional degree of protection and visibility for your Kubernetes installations.
Tools like AWS Security Hub, Microsoft Defender for Cloud, and Google’s Security Command Center help teams identify threats, respond to incidents, report compliance, and carry out security analytics.
Needless to say, they’re essential for increasing Kubernetes security in multi cloud environments. However, the vast majority of them just cover a subset of security, whereas deployments most often demand a more comprehensive plan.
Container security tools
There are other tools available that provide a variety of capabilities to strengthen the security of your Kubernetes setups.
One helpful feature is vulnerability scanning, which detects flaws across your cluster.
You should also consider getting a tool that scans your cluster configuration to make sure it’s in line with industry best practices that directly relate to its security.
Ensure multi cloud Kubernetes cluster security with automation
The Kubernetes ecosystem and its security and configuration components are constantly evolving. Keeping up with these changes takes time and effort, diverting engineers’ focus away from other activities that demand it.
And even if you find some vulnerabilities or misconfigurations, you’ll have to take the time and prioritize them. Depending on the scale of the application, this activity can become time-consuming.
But automation is about to change all of that.
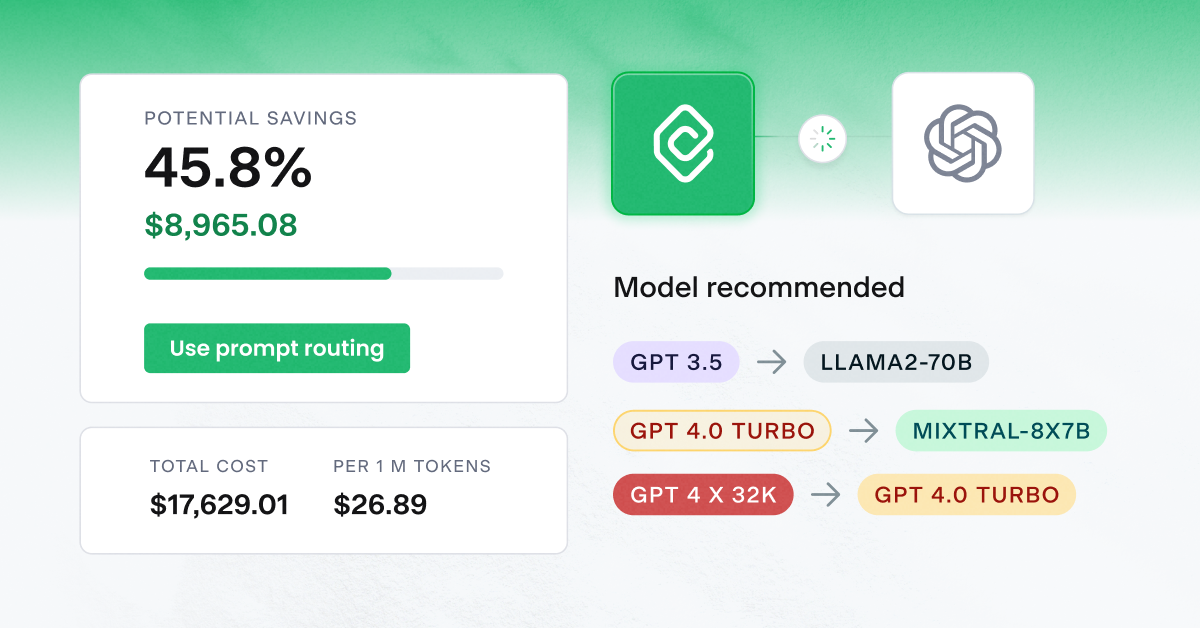
CAST AI’s Cloud Security feature scans clusters against industry best practices, Kubernetes guidelines, and container security system benchmarks – and prioritizes them automatically to help you standardize security across all cloud providers.
// get started
Optimize your cluster for free
Try powerful Kubernetes automation features combined with full cost visibility via cluster-specific savings reports and cost monitoring.
No card required
Unlimited clusters
Instant savings insights
FAQ
Kubernetes Multi Cloud Cluster Security refers to the practices and tools used to ensure the security of Kubernetes clusters deployed across multiple cloud platforms. This includes securing the control plane, worker nodes, containerized applications, and data in transit and at rest.
Secure communication between clusters can be achieved using mutual TLS (mTLS), network policies, and service mesh solutions like Istio or Linkerd. Additionally, using VPNs or dedicated interconnects provided by cloud providers can further enhance security.
Role-Based Access Control (RBAC) is a native Kubernetes feature that allows you to define who can do what within a cluster. For multi cloud deployments, centralized identity providers integrated with all cloud platforms can help manage access consistently.
Multi cloud deployments can introduce complexity, which can lead to misconfigurations. Common vulnerabilities include exposed dashboards, lack of network segmentation, and misconfigured RBAC. It’s essential to regularly scan and audit your configurations and use tools like Kubernetes security benchmarks to identify potential risks.
Data encryption in transit and at rest is crucial. Use cloud provider-native tools and third-party solutions to encrypt data. Additionally, ensure that you have logging and monitoring in place to track data access and movement. For compliance, consider tools that provide multi cloud compliance checks and reporting.



Leave a reply