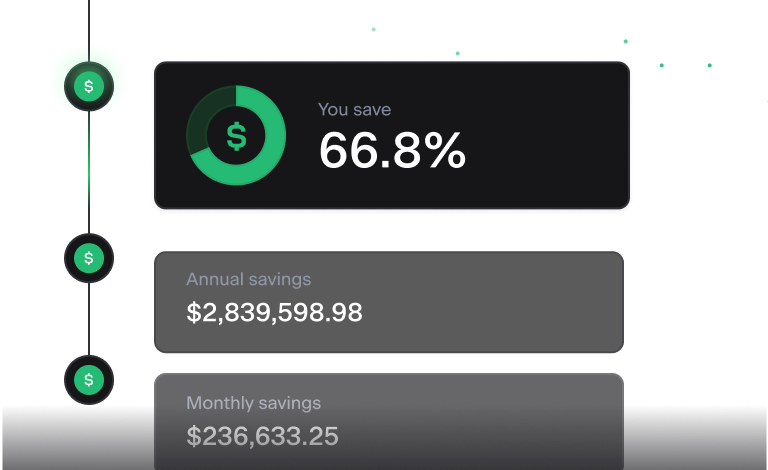
Cut your cloud cost in half
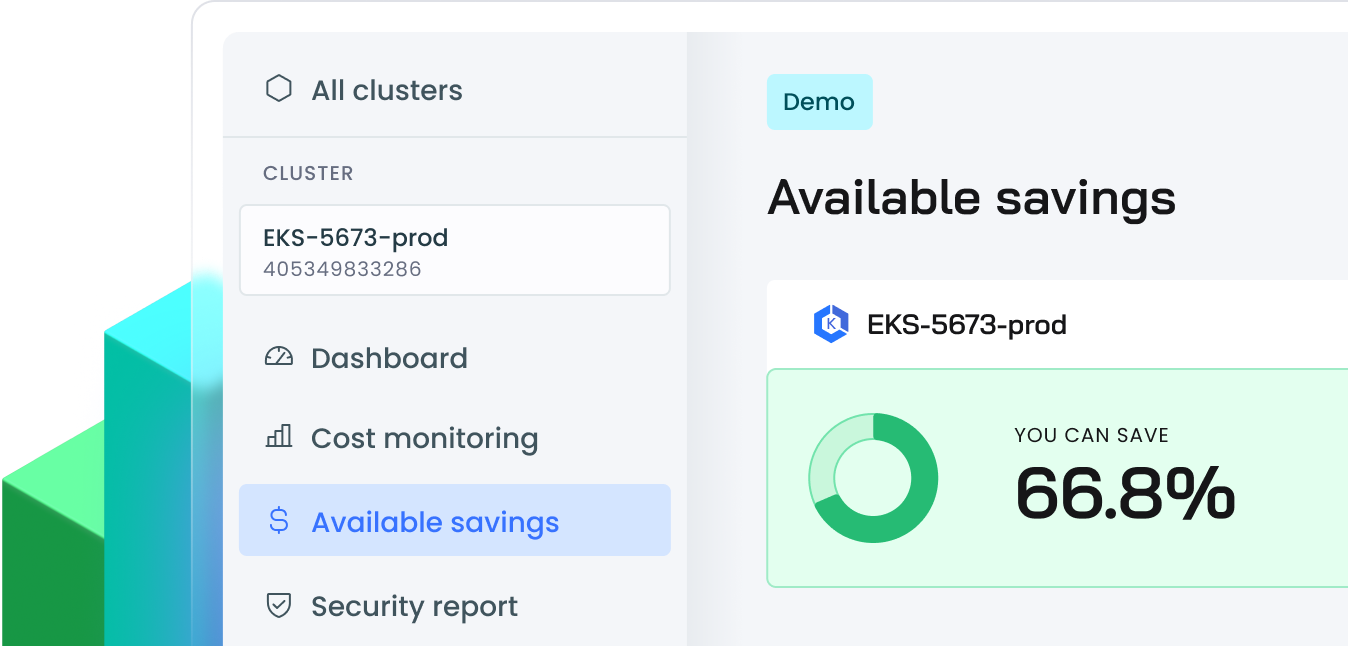
CAST AI is the leading Kubernetes automation platform that cuts AWS, Azure, and GCP customers’ cloud costs by over 50%.
Trusted by the world’s leading brands
Key features
Discover a fully automated Kubernetes experience
CAST AI continuously monitors your cluster and applies changes in real-time to keep your configuration optimal.
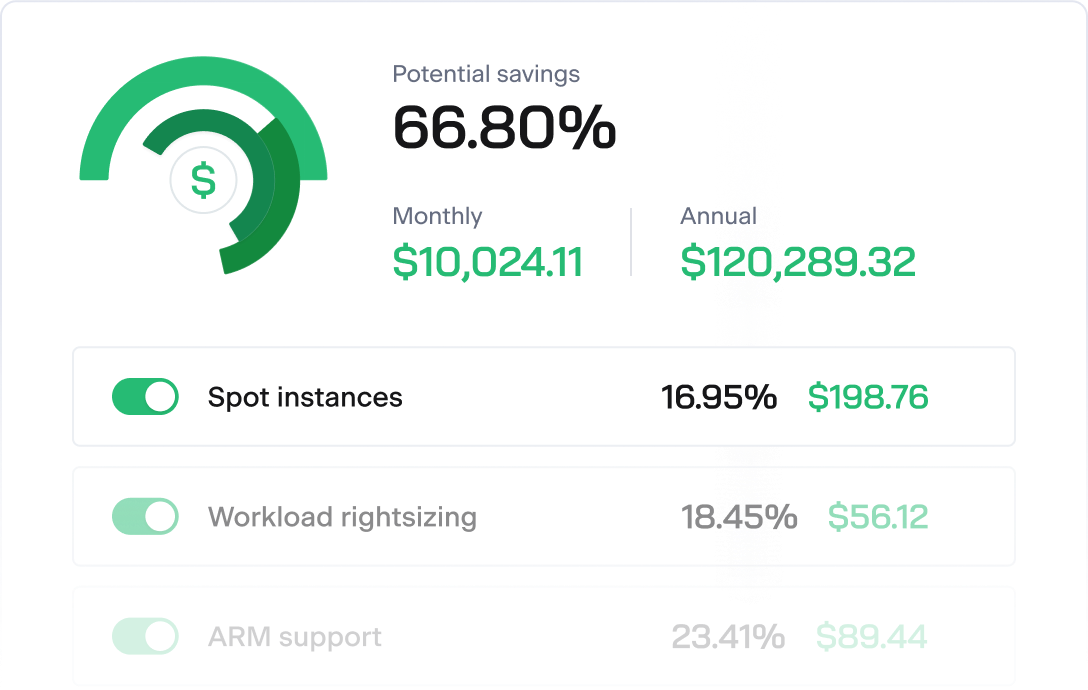
Cloud cost optimization
Cut your K8s costs in half by having your clusters continuously tracked and optimized with features like automated scaling, provisioning, bin packing, and more.
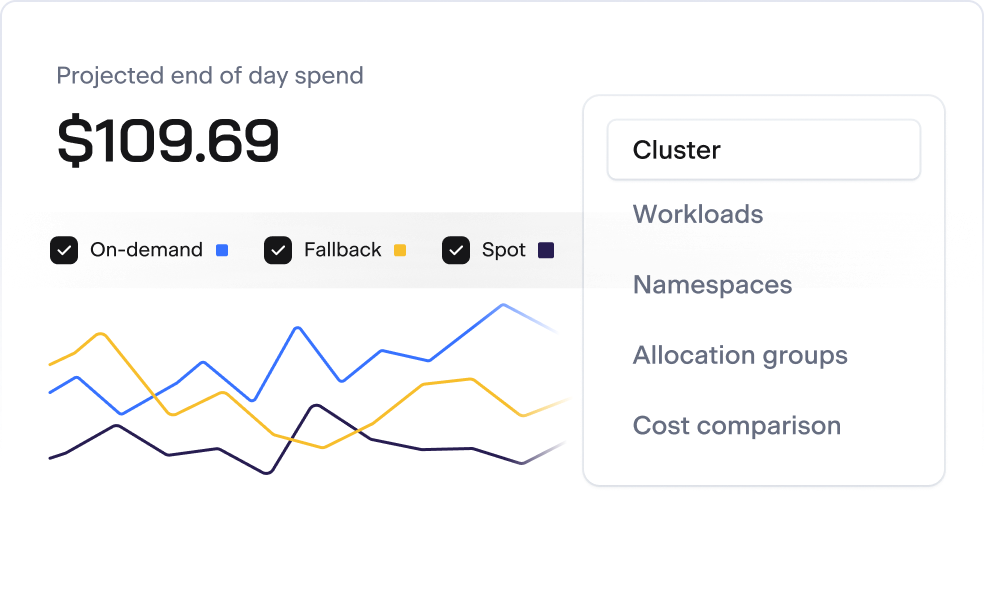
Kubernetes cost monitoring
View all your expenses in one place, monitor them in real time, and break them down by cluster, workloads, labels, and other K8s concepts.
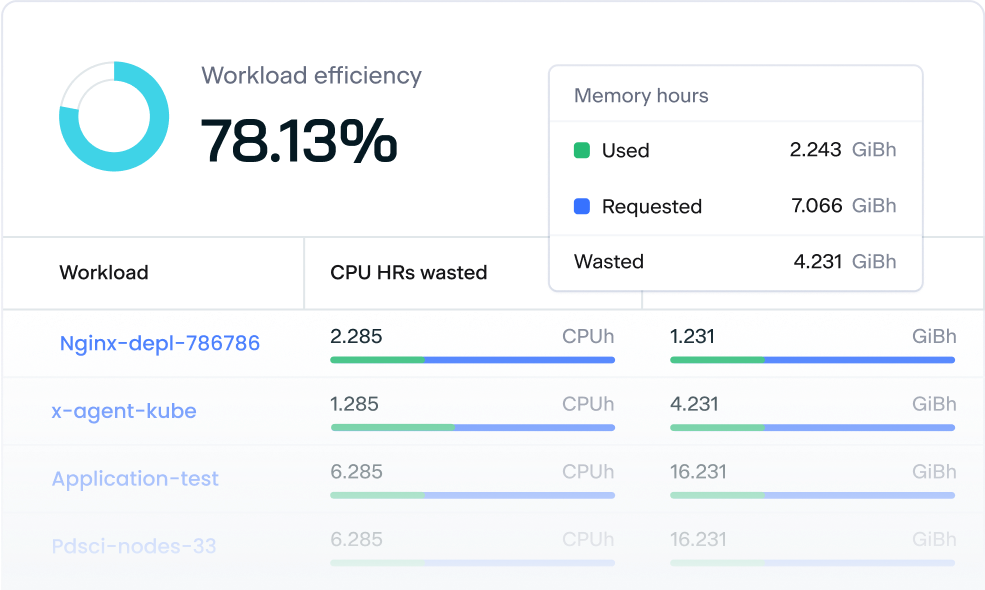
Workload rightsizing
Automatically adjust your workload’s requests and limits to
match its changing needs and achieve an optimal cost-performance ratio.
Partners and integrations
Join our powerful cloud ecosystem
CAST AI seamlessly integrates with key technologies, letting your customers optimize K8s cost management automatically.
See it in action
Explore all the capabilities of CAST AI.
Play with a demo cluster or watch a video demo session now.
How project44 achieved 50% cost savings within a month
“The cost optimization features have a massive business impact. For any large-scale deployment, I think that it would be silly not to look into CAST AI very seriously”

Olivier Modica
VP of Engineering
How the social giant ShareChat is saving millions while reducing engineer effort
“The cluster scales up and down with the right optimized configuration when needed, ultimately saving Sharechat millions in our Kubernetes infrastructure.”

Jenson C S.
Engineering Manager
How Iterable saved $3M on Amazon EKS with automation and cost visibility
“Even 1 or 3% of a massive AWS bill is significant. So when you say numbers like 20% people are losing their minds. And our total possible savings take that 20% closer to 60 or 70%, which translates to $3-4 million per year.”

Jason Sanghi
Staff Software Engineer
How Ampeers Energy saved 33% on AKS
“After we configured everything to be in line with industry best practices, it was really just a single meeting. We pressed a button, waited for 30 minutes, and after that, everything was done. We saw a 33% cost reduction on the cluster connected to CAST AI.”

Lukas Marquardt
DevOps Engineer
How NielsenIQ saved up to 80% on cloud costs with automated node provisioning
“Anybody – from small, mid to large firms – can benefit from the cost savings CAST AI generates. It will probably pay for itself within the first month or two. And after that, it keeps saving you money.”

James O’Hare
Principal Platform Engineer
Overview
For FinOps and DevOps alike
Get on top of your Kubernetes spend and automate cloud operations with CAST AI features.
All-in-one plaform
Benefit from cost monitoring, autoscaling, and workload rightsizing that function as one cohesive unit.
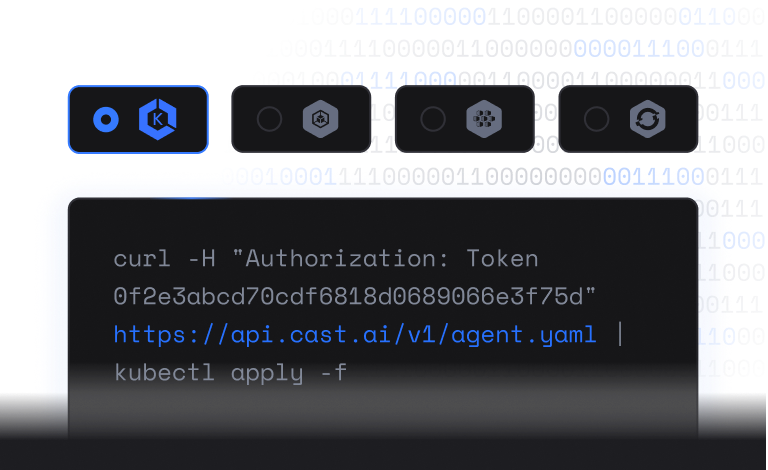
Frictionless onboarding
Running one script is all you need to get started. A proof of concept takes just a week on average.
Automated savings
CAST AI works 24/7 to slash your Kubernetes spend without sacrificing uptime or performance.
Developer‒friendly
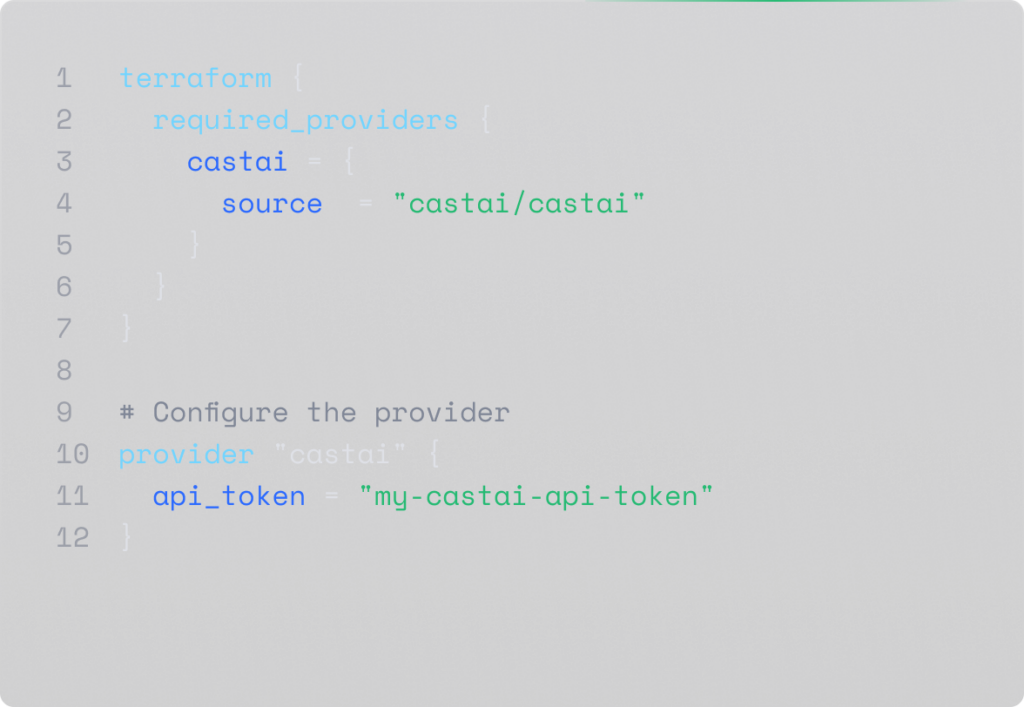
Engineering hub
Check out our documentation and API reference to learn how to maximize your K8s efficiency and savings with automation.
Third-party integrations
Recent articles
CAST AI in the news
“Organizations often provision double the number of servers needed in the cloud. Kubernetes is the most common use case for cloud cost optimization because often developers just eyeball the amount of CPUs they need, over-provisioning just in case there’s a traffic spike.”
“The expense of keeping the [application] running goes from thousands of dollars to millions. And the reason is: over or under-provisioning of resources. The manual effort to manage the resources just doesn’t work well enough to save money.”
“What CAST AI provides is their customers’ ability to benefit from substantial cost optimization in managing their cloud expenses. CAST AI determines how much you can save, then reallocates your cloud resources in real time to hit the target with no impact on performance.”
What’s new
Highlights and insights
-

CAST AI Appoints Pierre-Andre Liduena as Chief Financial Officer
Pierre will oversee corporate strategy and financial operations, playing a pivotal role in CAST AI’s next chapter…
-
CAST AI Automatically Reduces the Cost of Deploying Generative AI
New AI Optimizer service automatically identifies the LLM that offers the most optimal performance and lowest inference…
-
How We’re Using AI to Optimize AI
Today CAST AI introduced a series of new features into its platform, designed to help optimize GPU-heavy…
-
CAST AI Unveils Interactive Map That Showcases Spot Instance Availability, Reliability, and Cost-Effectiveness By Cloud Provider
The Spot Instance Availability Map enables DevOps teams to assess the risks associated with using Spot instances…
Start saving on cloud today
CAST AI slashes 50%+ of your Kubernetes spend without sacrificing uptime, performance, or DevOps time.